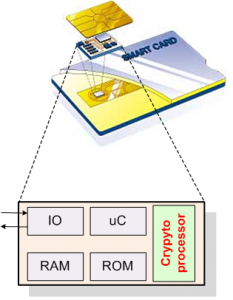
The problem this project proposes to solve is significant and critical. Recent changes in usage models of emerging sensitive applications using deeply-embedded systems, e.g., implantable and wearable medical devices, Internet of nano-Things, and extremely-constrained smart cards, call for new and practical security mechanisms. Unfortunately, adopting the traditional security and cryptographic solutions often either fails in providing the required security properties or exhibits sub-optimal efficiency. In fact, in addition to exhibiting security, crypto-systems need to be feasible to utilize as well for applications in which performance and implementation metrics are bottleneck, without jeopardizing the security properties needed. Due to this order change in constraints, new cryptographic algorithms and architectures (and not those providing incremental performance and battery-life alleviations) are needed. The aforementioned is the motivation in this proposal whose outcome is envisioned enabling security for emerging usage models which outperforms current solutions.
In this project, the we provide coherent crypto-solutions feasibly applicable in practice through identifying three main levels of computations: finite field arithmetic, group operations, and point multiplication. The PIs also propose new approaches for computing point multiplication on binary elliptic curves using endomorphisms and differential addition chains. The outcome of this proposal is envisioned to protect emerging, sensitive infrastructures, for both resource-constrained and high-performance applications. The goal of this proposal is to establish a paradigm shift in security, reliability, and energy-efficacy of sensitive embedded systems.
[/vc_column_text][/vc_column][/vc_row][vc_row][vc_column css=”.vc_custom_1498197625181{padding-right: 55px !important;padding-left: 55px !important;}”][vc_tta_accordion][vc_tta_section title=”Publications” tab_id=”1497932974627-8fc49713-5a31″][vc_column_text]
- K. Järvinen; A. Miele, R. Azarderakhsh, P. Longa, “FourQ on FPGA: New Hardware Speed Records for Elliptic Curve Cryptography over Prime Fields”, in Proc. CHES 2016, pp. 517-537, LNCS, vol. 9813, Aug. 2016.
- R. Azarderakhsh and K. Karabina, “Efficient Algorithms and Architectures for the Computation of Double Point Multiplication on Elliptic Curves”, in Proc. Third ACM workshop on Cryptography and Security in Computing Systems, CS2@HiPEAC 2016, ACM, pp.25-30, Jan. 2016.
- B. Koziel, R. Azarderakhsh, and M. Mozaffari Kermani, “Low-resource and fast binary Edwards curves cryptography using Gaussian normal basis” in Proc. IndoCrypt 2015, pp. 347-369, Dec. 2015.
- R. Azarderakhsh and K. Karabina, “A New Double Point Multiplication Algorithm and its Application to Binary Elliptic Curves with Endomorphisms“, IEEE Transactions on Computers, vol. 63, no. 10, pp. 2614-2619, 2014.